Data Security with Flex2SQL and BTR2SQL Connectivity Products
The most common reason for Enterprises looking to migrate from legacy Btrieve or DataFlex databases is the urgent need to address security and...

The October 2017 version of Thriftly provides support for JSON Web Tokens. JSON Web Tokens (JWTs) are an open standard method for authorizing users and transmitting information securely using metadata embedded directly in your API calls.
JWTs are compact and self-contained, meaning authorization is fast and doesn’t require your server to maintain session data or route calls through a separate authorization layer. With Thriftly, all it takes is a few simple steps to create truly stateless APIs with built-in JWT authorization.
In this post, we’ll get into how JWTs are commonly used, what JWTs look like, and how to implement JWTs in Thriftly.
JWTs are primarily used to authorize users post-login and ensure transmitted information hasn’t been tampered with in transit.
With Thriftly (or any other service that provides JWTs), when a user initially logs in, Thriftly passes that user a unique JWT that contains several claims (pieces of unique, identifying information). This JWT is then embedded in the header of the user’s subsequent API calls, and the Thriftly API server itself (not a separate table containing session data) decodes the JWT to verify the user’s identity and ensure that the API call was not modified in transit. Using this stateless authorization method reduces the number of calls needed for each API request, significantly reducing server overhead while keeping requests secure.
You can view an example: 5 Easy Steps to Understanding JSON Web Tokens (JWT) / (after clicking the link, scroll to the first diagram).
Above, we said JWTs are compact. In this section, we’ll explain what that means, and why it’s important.
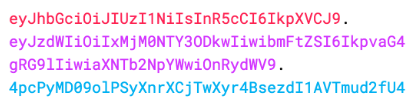
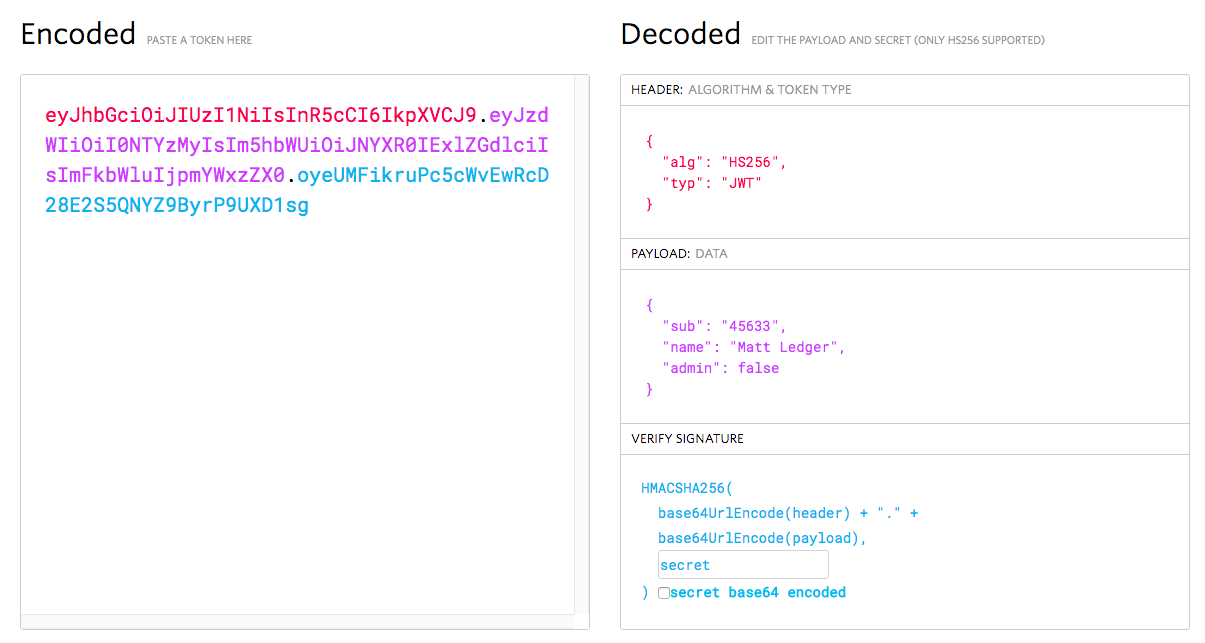
JWTs contain just three components: a header, a payload, and a signature.
This, finally, creates an encoded JWT:
![]()
When your application server receives an API call containing this token, it works backwards, using the key and the hashing algorithm you’ve chosen to decode the JWT and verify that the user is who she says she is and that her API call wasn’t tampered with in transit. If your application can’t successfully decode the JWT, it throws an error and rejects the call.
JWTs’ simple structure is one of their greatest strengths. Because JWTs use a simple JSON structure, composed of just three parts, they are easy to encode and decode, further speeding up the authorization process.
As part of developing and deploying your Thriftly APIs, you can configure them to generate and require JWTs. Thriftly handles the majority of the work for you, generating and verifying JWTs largely as described above. There are just a few simple things you have to do to turn on JWTs in Thriftly and secure your APIs.
First, you must update your Thriftly APIs to create and require JWTs.
You do this by:
Second, you can choose from several hashing algorithms, including ES256 and HMAC384, to determine how Thriftly encodes and decodes JWTs:
Third, you can use Thriftly to generate the keys used to decode your JWTs:
Detailed documentation walking you through exactly how to implement JWTs in Thriftly is available in the Thriftly docs (Configuring Your APIs to Handle JSON Web Tokens), but we wanted to tell you about this new feature here so you could get started experimenting with JWTs! If you have any questions, feel free to leave them as a comment below, and a Thriftly developer will get back to you.

The most common reason for Enterprises looking to migrate from legacy Btrieve or DataFlex databases is the urgent need to address security and...

Introduction Many independent software vendors (ISV) and corporate users still rely on applications that use a category of database collective called...

COBOL applications are the foundation of numerous essential business functions, especially within the banking, insurance, and government sectors....